A 30-year-old Sudanese man was charged with attempted murder on Tuesday after a stabbing in Belfast, sparking violent anti-immigration protests across the city. Masked crowds torched homes, cars, and a Glider bus, while officials condemned the “thuggery” as far-right figures amplified the unrest via social media.
Could cave bacteria help cure cancer? A USU discovery suggests they might
Ryan Jackson, an associate professor of biochemistry at Utah State University, has identified a CRISPR nuclease called Cas12a2 from cave bacteria that could potentially cure cancer. According to UPR, the tool can be programmed to selectively destroy cancer cells while leaving healthy tissue intact.
The Cas12a2 DNA-Shredding Mechanism
Most people recognize CRISPR as a tool for genetic editing, specifically the Cas9 protein adapted for eukaryotic cells in 2012. While Cas9 acts like a pair of molecular scissors to cut and edit DNA, the newly discovered Cas12a2 operates with a different, more aggressive objective. In nature, CRISPR serves as a bacterial immune system used to fight viruses. This system uses a protein component and an RNA component to recognize and attack genetic invaders. However, Cas12a2 doesn’t just edit a sequence; it triggers a systemic collapse within the targeted cell.Ryan Jackson, associate professor of biochemistry at USUThis “shredding” capability transforms the protein from a surgical tool into a weapon. By programming the guide RNA to match the genetic sequence of a cancer cell, researchers can theoretically trigger this rampage only within malignant cells, bypassing the healthy ones.
Solving the Chemotherapy Side-Effect Problem
The primary struggle in oncology is the lack of precision. Traditional chemotherapy is essentially a carpet-bombing campaign; it kills cancer cells, but it also destroys healthy cells, leading to the severe side effects associated with the treatment. Jackson describes the ability to manipulate one specific target without affecting others as a “Holy Grail” in medicine. The distinction lies in what the tool “sees.” While many therapies rely on external markers, Cas12a2 targets the internal genetic code.By focusing on the internal genetic differences, this approach aims to eliminate the collateral damage that characterizes current cancer treatments.“We’re not going off of what’s on the outside,” Jackson said. “We’re going off of what’s on the inside, and what’s on the inside is very different. We’re going after that genetic difference that makes it cancer.”
Ryan Jackson, associate professor of biochemistry at USU
Bacteria as Targeted Cancer Delivery Systems
The use of bacteria to fight tumors isn’t entirely new, but the mechanisms are evolving. According to a review published by PMC, researchers have previously used genetically engineered strains of Salmonella and Clostridium butyricum M55 in mice to deliver toxins that destroy tumors. These earlier methods focused on using recombinant DNA technology to make bacteria release toxic chemicals or activate the host’s immune system via cytokines. The emergence of Cas12a2 adds a layer of programmable precision that previous bacterial therapies lacked. The stakes for these advancements are high. The PMC report notes a grim projection: cancer-related deaths are predicted to reach approximately 20 million by 2030. This trajectory has accelerated the search for alternatives to radiation and chemotherapy, particularly as tumors develop drug resistance.The Genetic Advantage of Cave Bacteria
The discovery of Cas12a2 highlights why isolated environments, like deep caves, are biological goldmines. Bacteria in these regions often evolve unique survival mechanisms due to their extreme isolation. For instance, research detailed by the BBC into *Paenibacillus sp LC231* found that these cave-dwelling microbes possess resistance genes that have never been encountered before in other environments. This suggests that isolated bacterial colonies can develop sophisticated biological tools—whether for antibiotic resistance or immune defense—that are entirely different from those found above ground. Jackson noted that while he didn’t know specifically that he would find a cancer-fighting tool, he began his work at Utah State with the conviction that bacterial immune systems could hold new biotechnological breakthroughs.Clinical Outlook and Limitations
While the data suggests that Cas12a2 can differentiate between cell types based on genetics, the transition from a laboratory discovery to a clinical cure requires significant work. The current success is a proof-of-concept: the ability to say, “I want to only kill this type of cell, but leave these other ones alone.” The next phase of development will likely focus on delivery mechanisms—how to get the Cas12a2 system into the human body and specifically into the tumor site without the body’s own immune system destroying the tool before it can work. If successful, this represents a shift from managing cancer to eradicating it at the genetic level. Consult your healthcare provider for medical advice regarding cancer treatments.Hidden homeless women are being missed from official figures, charities warn
Research from Solace Women’s Aid and Single Homeless Project reveals that nine out of 10 homeless women are missing from official UK government figures. The charities report that gender-biased collection methods overlook women who avoid visible rough sleeping to escape gender-based violence, sheltering instead in cafes, hospitals, and on public transport.
The discrepancy between official counts and reality
The Ministry of Housing, Communities and Local Government relies on rough sleeping snapshots that fail to capture the specific ways women experience homelessness. According to reporting by Yahoo News, the government counted 680 women across 296 local authorities who were rough sleeping in 2024. However, Census Local Insights meetings identified 1,777 women across only 37 local authorities during that same year. This gap suggests a systemic failure in how the state identifies vulnerable populations. Lucy Campbell, head of multiple disadvantage at Single Homeless Project, has characterized the current methodology as asystemic failure, arguing that the government must overhaul how it counts homeless women to ensure they are not erased from policy and funding decisions. The failure is largely numerical and spatial. Roughly 54% of homeless women are excluded from official statistics because they spend their nights in locations not classified as rough sleeping areas. These include:
- A&E departments
- Bank foyers
- Public transport (buses and trains)
- 24-hour cafes
Safety drivers and the choice of invisible shelter
Women are significantly less likely tobed downvisibly on the street compared to men, primarily due to the threat of gender-based violence. To survive, many seek out environments that offer a balance of seclusion and public visibility. “This is typically where you would find women, maybe more in the day, maybe in the night as well. It’s somewhere quite secluded, still tucked away in the corner. But also, you’re still in public. So if something happened and you felt like your safety was at risk, you could still make some noise.” Elise Godsal, specialist women’s navigator at Single Homeless Project The risks of visible homelessness are visceral. One woman, Nadia, told reporters she once slept outside a Santander bank and woke up being
kicked in the head. Her experience highlights a pattern of extreme vulnerability, as she recounted being
pissed onand forced to make a home out of a cardboard box in car parks or bin sheds. As Smitfc.org notes, this invisibility is often a survival strategy. Women may engage in sofa surfing, stay in exploitative relationships to avoid the street, or hide their substance use and abuse to avoid being judged or losing their children.
Systemic failures in homelessness accommodation
The lack of visibility is not merely a result of where women sleep, but a reflection of a support system that fails to protect them. The 2024 Women’s Rough Sleeping Census report found that 37% of women had been in some form of homelessness accommodation before they began sleeping rough. This suggests that existing shelters and temporary housing are not meeting women’s specific needs or preventing the slide into rough sleeping. The choice for many is not between a home and the street, but between two different types of danger. “Many women face a really stark choice between remaining in abusive environments and abusive homes, or risking entering a homelessness system that can sometimes be just as harmful, and where the very systems meant to protect them, often let them down, or, worse, expose them to further harm.” Source: Solace Women’s Aid and Single Homeless Project research For some, the only perceived safety is found in unconventional alliances. One survey respondent reported being raped while sleeping in a bank doorway and now ensures she is with a male rough sleeper at all times, noting that while it is thesafest option, it does not mean she is actually safe.
Localized evidence from the Leeds Census
National trends are mirrored in regional data. The 2024 Leeds Women’s Rough Sleeping Census, facilitated by Basis Yorkshire, surveyed over 70 women to understand the local landscape of hidden homelessness. Amber Wilson, Business Development and Marketing Manager at Basis Yorkshire, indicated that her research backs up national findings. The Leeds data showed women spending nights walking around the city, staying in 24-hour venues like McDonald’s, or relying on the unpredictable kindness of strangers for shelter. The synthesis of these reports indicates that the UK’s current approach to homelessness is designed around a male-centric model of visibility. By focusing on those sleeping in the open, the state ignores the thousands of women who must remain invisible to survive. Without a shift toward gender-specific services and tailored pathways, these women remain excluded from the funding and support required to break cycles of trauma and instability.Wembanyama Condemns Violence Against Spurs Fans After NYC Postgame Chaos
Victor Wembanyama and several NBA players condemned violence against San Antonio Spurs fans following postgame altercations in New York City on Monday. After the Spurs’ 115-111 Game 3 victory, reports emerged of Spurs supporters being harassed and attacked, leading to 21 people being taken into police custody in the surrounding areas.
Postgame Chaos and Arrests in New York City
The tension following the Spurs’ redemptive victory at Madison Square Garden boiled over into the streets of Manhattan. As The Guardian reported, videos circulating on social media showed Spurs fans having their jerseys ripped off and being mobbed by crowds in the aftermath of the game. The violence was not limited to a single location. Reports indicated that a fan watch party at Bryant Park unraveled into a fight that led to more than 20 arrests, according to Fox News. According to CBS News, a total of 21 people were taken into police custody, with eight arrests confirmed in connection with the violence related to the NBA Finals. The chaos occurred on a night when security was already heightened; one watch party outside Madison Square Garden had been canceled due to the attendance of Donald Trump.Wembanyama and Towns Demand Player-Fan Respect
Spurs star Victor Wembanyama, who finished Game 3 with 32 points, eight rebounds, and six assists, expressed shock when informed of the street attacks during media availability on Tuesday.“My thoughts, of course, is that we can’t forget it’s a game. We’re just playing a game out there. And I am all for passion, but, to the respect of each other, it’s unacceptable.”


“I mean, the game is built off respect and passion. We want everyone to respect each other. We want everyone to enjoy basketball at its pure state. I mean, it’s the NBA Finals. There’s no better place to watch basketball. So leave the physicality to everyone on the court.”
Karl-Anthony Towns, via sports.yahoo.com The plea for decorum was echoed by prominent New York Knicks supporters. Ben Stiller, a regular courtside attendee, took to X on Tuesday to state that being a Knicks fan does not necessitate disrespect toward Spurs supporters.Champagnie and Johnson Address Fan Safety
For Spurs forward Julian Champagnie, the situation was personal. A New York native, Champagnie was asked on Tuesday if he felt threatened by the atmosphere in the city following reports that San Antonio head coach Mitch Johnson and his family had been heckled. Speaking to mysanantonio.com, Champagnie noted that while he did not feel a direct threat, the escalation of fan behavior was unwarranted.“I don’t really feel no threat. I’m from here, so I feel like a lot of this stuff is kind of just like what it is. You get used to it. So I don’t know about threat, but I think that, obviously, we’re here to play a basketball game. That’s the main thing. For the fans, I don’t think that it should ever be that serious, where you have to jump people, beat people up, follow people home and stuff like that.”
“Obviously, we’re competing at a high level, competing for a championship, but we don’t want to sacrifice safety over a game we love. We go out there and compete every night, and we value safety. I feel that’s one through 15 on this side and one through 15 on that side.”
Keldon Johnson, via mysanantonio.comKnicks Series Lead and Upcoming Schedule
Despite the off-court distractions, the series remains a high-stakes battle between two storied franchises. The Knicks currently lead the series 2-1 as they chase their first NBA championship since 1973. The teams return to Madison Square Garden on Wednesday, June 10, for Game 4. Following the New York leg of the series, the Finals will move to San Antonio for Game 5 on Saturday, June 13.Українська гімнастка, яка втратила ногу після ракетного обстрілу, виграла міжнародний турнір у Румунії. Відео
Oleksandra Pascal, a 9-year-old gymnast from Chornomorsk, won a gold medal at the Carla’s Rhythmic Cup in Brasov, Romania, from June 5 to 7, 2026. Pascal returned to international competition after losing her leg during a Russian missile strike in May 2022, marking a significant athletic recovery.
Gold Medal in Brasov
The victory at the Carla’s Rhythmic Cup represents more than a podium finish for the young athlete. Judges at the event praised Pascal’s technical skill, artistry, and the overall quality of her program execution, according to Obozrevatel.
Oleg Kiper, the head of the Odesa Regional Military Administration, highlighted the win as a testament to the girl’s resilience. As reported by Yug Today, Kiper noted that the audience applauded not just her skill, but her internal strength.
“At the prestigious ‘Carla’s Rhythmic Cup’ tournament in Romania, a young gymnast from Chornomorsk won a gold award.” — Oleg Kiper, Head of Odesa Regional Military Administration
Pascal’s return to the international stage is a rare feat in rhythmic gymnastics, a sport that demands extreme flexibility, agility, and balance. The discipline requires athletes to perform complex routines involving apparatus such as the hoop, ball, clubs, and ribbon, often combining elements of ballet and gymnastics. These requirements are severely challenged by the loss of a limb, as the sport relies heavily on precise weight distribution and pivot movements to achieve high scores from judges.
The May 2022 Strike in Zatoka
The trajectory of Pascal’s life shifted on May 16, 2022. According to Ukrinform, Russian forces launched a missile strike on a vacation base in the Bilhorod-Dnistrovskyi district, specifically in the village of Zatoka.
Zatoka is a seaside resort area in the Odesa region, often targeted due to its strategic location and infrastructure. The attack occurred around 9:00 a.m. while Pascal’s family was inside the home. The resulting collapse of a ceiling slab crushed her leg, destroying the bone. The 5-year-old suffered a cascade of critical injuries:
- An open fracture of the arm
- A head injury
- Four broken ribs
- Multiple shrapnel wounds
Medical teams held Pascal in a medically induced coma for 15 days to stabilize her condition and manage the trauma. Despite exhaustive efforts, doctors were unable to save her leg, resulting in amputation. Her mother, Maria Pascal, was also injured in the attack.
Rehabilitation and the Path Back
The road from a coma to a gold medal involved years of intensive medical intervention. After initial treatment in Ukraine, Pascal traveled to Austria for specialized rehabilitation. This phase of her recovery was critical, as it transitioned from life-saving surgery to functional restoration.
In Austria, she underwent surgery on her arm to insert special pins, which remain in place today. She also received a prosthesis and spent four months relearning how to walk. For an aspiring athlete, this process involves more than basic mobility; it requires retraining the brain and body to maintain balance and coordinate movements with a prosthetic limb, a process known as prosthetic integration.
Immediately upon returning to Ukraine, Pascal resumed her training in rhythmic gymnastics. Before the 2022 strike, she had already been active in dance and gymnastics, earning various awards. This existing foundation of muscle memory and athletic discipline likely accelerated her ability to adapt her routines to her new physical reality, allowing her to modify her movements to accommodate the prosthesis while maintaining the artistic standards of the sport.
National Recognition and Future Outlook
Pascal’s recovery has transitioned from a personal victory to a national symbol. At the end of 2025, President Volodymyr Zelenskyy awarded her the State award “Future of Ukraine,” as noted by Rubryka. This state recognition is typically reserved for young citizens who demonstrate exceptional courage, resilience, or achievement in the face of the hardships brought by the ongoing conflict.
Her competitive timeline shows a steady climb back to peak form:
| Year | Milestone |
|---|---|
| 2022 | Injury and amputation following Zatoka missile strike |
| 2023-2024 | Rehabilitation in Austria; learning to walk with prosthesis |
| 2025 | Participation in first post-injury competitions at age 7 |
| 2025 (Late) | Receipt of “Future of Ukraine” State award |
| 2026 | Gold medal at Carla’s Rhythmic Cup in Romania |
The victory in Romania proves that the physical limitations imposed by war-time injuries can be overcome through a combination of high-level medical care and psychological resilience. For Pascal, the gold medal is not just a sporting achievement, but a reclamation of an identity nearly erased by the 2022 attack.
Jurrien Timber will miss the 2026 World Cup after failing to recover from a groin injury, the Royal Dutch Football Association (KNVB) announced Monday. The 24-year-old Arsenal defender left the team’s training camp in New York following a match against Uzbekistan, leaving coach Ronald Koeman to reorganize the defense before the tournament opens.
KNVB Medical Ruling and New York Departure
The decision to rule out Timber comes after a prolonged struggle with a groin injury that first emerged in mid-March. While the defender attempted to integrate back into the squad, the medical staff determined his recovery pace was insufficient for the demands of a major tournament. “Jurrien Timber has not made enough progress to participate in the tournament in a medically responsible way.” KNVB, via ANTARA News According to CNN Indonesia, Timber had already joined the Dutch delegation in New York for training. However, following consultations with medical personnel, the KNVB decided he would leave the camp immediately after the friendly match against Uzbekistan.The Club-Country Conflict: Arsenal and the Champions League Final
The timing of Timber’s absence highlights a tension between club priorities and international fitness. Timber was declared fit by Arsenal manager Mikel Arteta just before the Champions League final on May 30. He entered the match against Paris Saint-Germain (PSG) as a substitute in the 66th minute, playing through the end of the game and into extra time. Despite the appearance, coach Ronald Koeman suggested that the late-season minutes did not aid the defender’s recovery. While Koeman refused to publicly scapegoat the London-based club, he noted the contradiction in Timber’s fitness levels. “You cannot blame the club, and I do not want to. Even so, it is clear that the playing minutes did not help. If he were only to play one more match in the future, that might be possible. However, a major tournament is not in the plan.” Ronald Koeman, via detikSport Koeman further explained that Timber had been unfit for a significant period, with lingering symptoms that prevented him from reaching match readiness for the World Cup.Defensive Restructuring and the Call of Geertruida
To fill the void left by the 24-year-old, Koeman has called up Sunderland defender Lutsharel Geertruida. The move forces a late tactical reshuffle in the Dutch backline just days before the opening whistle in North America. The integration of Geertruida is viewed as a necessary step to provide stability and depth. While Timber’s versatility was a cornerstone of the national team’s strategy over recent years, Geertruida now enters the squad as the primary solution to maintain defensive cohesion in Group F.Gakpo’s Reaction and the Oranje’s Offensive Crisis
The loss of Timber has reverberated through the squad, particularly among the attacking core. Cody Gakpo, the Liverpool winger, described the defender’s absence as a significant blow to the team’s overall strength. “Of course everyone knows his quality. He is important for the team, so this is a big loss. But in the end, I think he is now doing what is best for his career.” Cody Gakpo, via Goal.com Gakpo’s concerns extend beyond the defense. Following a narrow 2-1 victory over Uzbekistan, Gakpo admitted that the Netherlands must become more clinical in the final third. He noted that the team has been unlucky with their final passes and choices in front of the goal. Gakpo currently holds 21 international goals. He is now eyeing the record held by Marco van Basten and Dirk Kuijt, both of whom scored 24 goals, while Rafael van der Vaart leads with 25.The Road Through Group F
The Netherlands enters the tournament in Group F, where they face a challenging slate of opponents. The squad must now prepare for a high-intensity start without one of their most versatile defenders. There is a slight discrepancy in reporting regarding the exact date of the opening match. CNN Indonesia reports the match against Japan takes place on Sunday, June 14, while ANTARA News lists the fixture for Monday, June 15, in Dallas. The group stage schedule for the Netherlands is as follows:- Match 1: Japan (June 14/15)
- Match 2: Sweden
- Match 3: Tunisia
Sophie Faucher, Quebec Actress and Host, Dies at 68 After Long Illness
Quebec actress, author, and host Sophie Faucher died Tuesday, June 9, 2026, at age 68 following a long illness, according to a statement from her talent agency. Faucher had been battling a recurrence of cancer that reappeared earlier this year, according to reports from La Presse and NoovoMoi.
Career Across Television, Film, and Theater
Faucher maintained a professional career spanning approximately four to five decades, appearing in television, film, and theater. According to NoovoMoi, she graduated from the Conservatoire d’art dramatique de Montréal in 1978 and began her television career in the early 1980s with Les fils de la liberté. The Conservatoire is widely recognized as a cornerstone of Quebec’s performing arts education, providing the rigorous classical training that has shaped generations of the province’s most prominent stage and screen talents.
In television, Faucher was recognized for her role as Crystale Bouvier-Montgomery in the series Le cœur a ses raisons, a character described by Radio-Canada as an ex-model. The series became a significant cultural touchstone in Quebec, utilizing satire to explore social archetypes and dynamics. Her other television credits include Dumas, Indéfendable, Virginie, Prozac, Les Mecs, and Discussions avec mes parents. She also served as a co-host for the Radio-Canada program Les lionnes alongside Chantal Lamarre and Suzanne Lévesque, and worked as a professor for Star Académie in 2009. The program is one of Quebec’s most prominent reality television formats, serving as a major platform for discovering new musical talent in the province.

Faucher’s film work included collaborations with directors Denys Arcand, Xavier Dolan, and Chloé Robichaud. These filmmakers represent the breadth of Quebec’s cinematic prestige, from Arcand’s internationally acclaimed social commentaries to Dolan’s modern, festival-winning narratives. Radio-Canada listed her film credits as Testament, Laurence Anyways, Pays, La Face cachée de la lune, and Ding et Dong, le film. Additionally, she contributed to the field of dubbing, providing voices for American actresses including Queen Latifah, Julie Christie, and Viola Davis. In the Quebec media landscape, dubbing is a specialized industry that ensures international productions are accessible to Francophone audiences through high-quality vocal localization. She also served as the narrator for the animated series Caillou, a globally recognized children’s program that contributed to her presence in the lives of young viewers across the Francophone world.
In the theater, Faucher performed works by Shakespeare, Molière, Musset, and Pirandello. These works represent the fundamental pillars of the classical dramatic canon, requiring a high level of technical mastery in both vocal and physical performance. She won a Gémeaux award in 2001 for her performance in Tohu-Bohu. The Gémeaux Awards, presented by the Académie des arts et des sciences du cinéma et de la télévision, serve as the primary accolades for excellence in Quebec television production.
Artistic Focus on Frida Kahlo and Maria Callas
Faucher developed specific artistic connections to the lives of Frida Kahlo and Maria Callas. NoovoMoi reported that in 2001, she wrote La Casa Azul, a play directed by Robert Lepage in which she portrayed Kahlo. Lepage is a globally influential director known for his multidisciplinary approach to theater and innovative staging. This production toured internationally for two years. Faucher also published several children’s books inspired by Kahlo and participated in the creation of the animated film Hola Frida, which was released in Quebec in 2025.
Her interest in Maria Callas also defined much of her recent work. After portraying the singer in Les Leçons de Maria Callas, Faucher co-wrote the 2023 book Une voix pour être aimée: Maria Callas. Her work on these biographical subjects allowed her to bridge the gap between historical research and dramatic performance. She continued to perform the role on stage alongside Marc Hervieux.
Family Legacy and Early Career
Faucher was the daughter of actress Françoise Faucher and the late director and playwright Jean Faucher. As the daughter of established artists, she was part of a lineage of performers within the Quebec cultural landscape. She was the sister of former sports journalist François Faucher.

Her entry into professional acting began at age 8, when she appeared in L’oiseau bleu alongside Marc Labrèche, according to Radio-Canada.
Recent Health Challenges and Professional Withdrawal
Faucher had previously fought a battle against cancer in the mid-2010s. According to La Presse and NoovoMoi, her health declined at the beginning of 2026 when the cancer returned.
In April 2026, Faucher withdrew from the production of the comedy Le duplex due to health reasons. The play was scheduled to feature Sylvain Marcel, Valérie Blais, and François Massicotte. While the production is expected to tour Quebec next summer—a common way to bring contemporary theater to regional audiences—Faucher’s departure was confirmed earlier this spring.
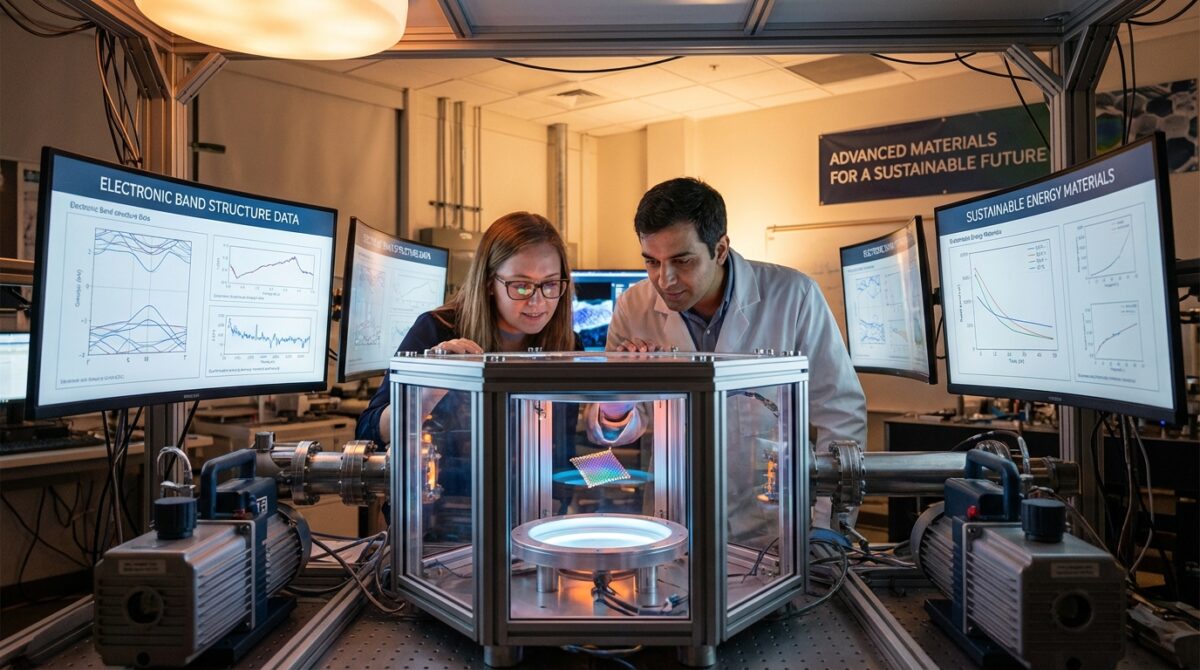
Researchers at the University of Washington are using artificial intelligence and quantum computing to accelerate the discovery of new materials. By combining machine learning models with quantum simulations, the university’s researchers aim to identify stable structures for semiconductors and battery components more efficiently than traditional methods allow, according to university research announcements.
Machine Learning and the Speed of Screening
The search for new chemical compounds requires simulating how atoms interact at a quantum level. This process typically uses Density Functional Theory (DFT), a method that requires high computational costs for complex systems. Machine learning models can approximate these interactions, allowing researchers to scan thousands of potential material candidates in a fraction of the time required by classical simulations.
Density Functional Theory operates on the principle that the ground-state properties of a many-electron system are determined by its electron density. While DFT is the standard workhorse in computational chemistry, it faces significant scaling issues. As the number of electrons in a system increases, the computational complexity grows, creating a “many-body problem” that can overwhelm even modern supercomputers when simulating large or highly complex molecular structures.
Machine learning addresses this bottleneck by acting as a surrogate model. Instead of solving the Schrödinger equation for every new candidate, researchers train neural networks on existing datasets of known material properties. These models learn to recognize patterns between atomic arrangements and their resulting physical characteristics, such as hardness, conductivity, or stability. This enables high-throughput screening, where a massive library of theoretical compounds can be filtered to identify the most promising candidates before any high-precision simulations are performed.
Quantum Algorithms and Electronic Precision
While machine learning speeds up the initial screening, quantum computing provides the precision needed for final verification. Quantum algorithms are designed to simulate the complex electronic structures of molecules, a task that often overwhelms classical hardware. This combination allows for the identification of materials with specific magnetic, electrical, or thermal properties.
Quantum computers utilize qubits, which can exist in superpositions that naturally represent the probabilistic nature of electron orbitals. This makes them theoretically superior to classical bits for simulating quantum mechanics. Current research in this area often focuses on hybrid quantum-classical algorithms, such as the Variational Quantum Eigensolver (VQE). VQE uses a quantum processor to calculate the energy of a specific molecular state and a classical processor to optimize the parameters, aiming to find the ground state energy—the lowest energy level at which a molecule is stable.
The precision offered by quantum simulations is critical for determining whether a theoretical material can actually exist under real-world conditions. While machine learning can predict that a structure is likely to be stable, quantum algorithms provide the mathematical rigor necessary to confirm the electronic configuration and the specific energy gaps that define a material’s behavior.
Potential Impact on Energy Storage
The ability to rapidly model new materials has implications for the energy sector. Research into these hybrid computational methods focuses on finding alternatives for lithium-ion battery components and developing more efficient semiconductors. Faster discovery cycles could reduce the time required to bring new energy storage technologies to market.
In the field of battery technology, the objective is to move beyond current lithium-ion limitations, such as energy density, charging speed, and safety concerns regarding thermal runaway. Computational modeling helps researchers explore new cathode and anode chemistries, as well as solid-state electrolytes, which could replace flammable liquid electrolytes. By simulating how ions move through a crystal lattice, researchers can predict which materials will offer higher capacity and longer cycle lives.
For the semiconductor industry, the focus involves discovering materials with wider bandgaps or higher electron mobility. These properties are essential for the next generation of power electronics used in electric vehicles and renewable energy grids, where components must operate efficiently under high voltages and varying temperatures.
The Hybrid Computational Workflow
The integration of these technologies creates a multi-tiered discovery pipeline. The workflow typically begins with broad, low-fidelity searches using machine learning to navigate the near-infinite space of possible atomic combinations. This stage filters out unstable or non-viable candidates, reducing the search space by several orders of magnitude.
The remaining high-potential candidates then undergo high-fidelity verification. This stage employs either traditional Density Functional Theory or, as hardware matures, quantum algorithms to perform deep-dive simulations of the electronic structure. This hierarchical approach minimizes the use of expensive computational resources, directing the most intensive calculations only toward the materials most likely to succeed in physical laboratory testing.
Technical Constraints and Hardware Limitations
The implementation of this hybrid approach faces ongoing technical challenges. Current quantum hardware is in the Noisy Intermediate-Scale Quantum (NISQ) era, meaning qubits are susceptible to decoherence and errors caused by environmental interference. These errors can limit the complexity and length of the quantum circuits that can be executed, making it difficult to simulate large molecules with high accuracy.
Additionally, the accuracy of machine learning models is strictly dependent on the quality and diversity of the training data. If the initial datasets are biased or limited to a narrow range of chemical elements, the models may fail to predict the properties of truly novel materials. Bridging the gap between the rapid approximations of machine learning and the high-precision requirements of quantum mechanics remains a central focus of ongoing research in computational materials science.
Shattuck Labs (NASDAQ: STTK) shares fell 4.22% after the biotech company announced a proposed public offering of common stock and pre-funded warrants, according to Stock Titan. The stock experienced a trough of -12.5% during tracking, as market participants reacted to the potential dilution of existing shares.
In the biotechnology sector, equity offerings are a common method for companies to secure the capital necessary to fund intensive research and development (R&D) cycles, clinical trials, and regulatory approval processes. Because these stages of development often require significant cash reserves before a product reaches commercialization, companies frequently utilize public markets to maintain liquidity.
Details of the Shattuck Labs offering
Shattuck Labs commenced a proposed public offering of common stock and pre-funded warrants for certain investors, according to Stock Titan. All securities in the offering will be provided by the company. Underwriters are expected to receive a 30-day option to purchase up to an additional 15% of shares.

The use of an over-allotment option, such as the 30-day option granted to underwriters, is a standard mechanism in equity offerings. This allows underwriters to sell more shares than originally planned if there is high demand, helping to stabilize the price and ensure the company meets its capital-raising goals.

The company is utilizing an effective S-3 shelf registration with a total capacity of $200,000,000. The registration statement for these securities was filed with the SEC on January 13, 2026, and the SEC declared the statement effective on January 21, 2026, Stock Titan reported.
A shelf registration, filed via an S-3 form, allows a corporation to register a large block of securities with the Securities and Exchange Commission (SEC) in advance. Once the SEC declares the registration statement effective, the company can “pull securities from the shelf” to sell to the market in multiple smaller transactions over time. This provides the company with the flexibility to time its capital raises based on favorable market conditions without the delay of a new registration process for each subsequent sale.
Market impact and trading activity
The announcement coincided with increased trading activity, with volume reaching 1.7x the average, according to Stock Titan. Following the news, the stock price was reported at $4.09, a movement that removed approximately $14 million from the company’s valuation. Stock Titan noted that the 4.22% decline reflected a moderate negative market reaction, while Argus tracked a trough of -12.5% from its starting point.
The spike in trading volume to 1.7 times the daily average suggests a significant increase in liquidity and investor repositioning following the disclosure. In equity markets, a sudden increase in volume paired with price volatility often indicates that institutional investors are adjusting their holdings in response to the new supply of shares entering the market. The trough of -12.5% indicates the maximum intraday downward pressure the stock faced as traders weighed the company’s need for capital against the immediate impact on share value.
The company’s market capitalization stands at $327.43 million, according to data tracked by Stock Titan.
Market capitalization, calculated by multiplying the current share price by the total number of outstanding shares, serves as a primary indicator of a company’s total market value. For mid-cap biotechnology firms, fluctuations in market capitalization are often sensitive to changes in capital structure, as the ability to fund long-term clinical milestones is directly tied to the company’s access to equity markets.
Potential shareholder dilution
The proposed equity offering presents risks to current investors. Stock Titan identified the new common stock and pre-funded warrants as a negative factor that could dilute existing STTK shareholders if the offering closes. While the offering enables a potential capital raise, the final size, pricing, and timing remain uncertain and subject to market conditions, Stock Titan reported.

Shareholder dilution occurs when a company issues new shares of stock, which increases the total number of shares outstanding. This increase results in existing shareholders owning a smaller percentage of the company than they did prior to the issuance. Dilution can also affect earnings per share (EPS), as the company’s total earnings are distributed across a larger number of shares.
The inclusion of pre-funded warrants in this offering is a specific structural choice. Pre-funded warrants are instruments that allow investors to purchase common stock at a predetermined price at a future date. These are frequently used in institutional offerings to allow large investors to participate in a capital raise while avoiding certain regulatory thresholds or ownership reporting requirements that are triggered when an investor holds a specific percentage of a company’s total outstanding common stock. While these warrants provide immediate capital to the company, they represent a future obligation to issue shares, which contributes to the “fully diluted” share count of the company.
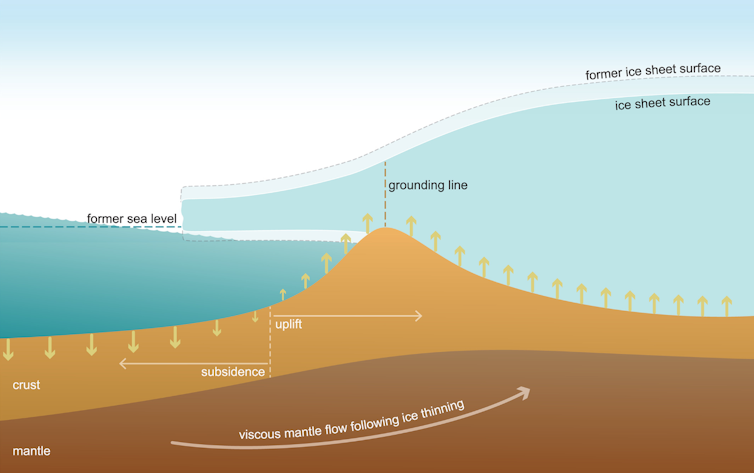
Falling sea levels during ice ages may increase volcanic activity and carbon dioxide emissions, potentially stabilizing atmospheric CO2 levels. Research led by the GEOMAR Helmholtz Centre for Ocean Research Kiel suggests that reduced pressure on the seabed during glacial periods enhances magma production, which could have influenced climate evolution 80,000 years ago.
How sea-level drops increase magma production
During glacial epochs, water evaporates from the oceans and is stored on continents as large ice sheets, ice caps, and mountain glaciers. According to the U.S. Geological Survey, this shift in the global hydrologic cycle causes sea levels to fall. This redistribution of water is a fundamental component of the Earth’s climate regulation; the movement of water from oceans to land-based ice changes the weight distribution across the planet’s crust, affecting the balance of the lithosphere and the underlying mantle. At the last glacial maximum approximately 20,000 years ago, global sea level was about 125 meters below today’s levels.
The mechanism driving this change is decompression melting. In the Earth’s mantle, high pressure keeps rock in a solid state even at high temperatures. When sea levels drop, the weight of the water column pressing down on the ocean floor is reduced. This decrease in lithostatic pressure allows the mantle to melt more easily, which enhances the production of magma.
ScienceDaily reports that this decreased pressure can enhance magma production, which in turn increases lava and carbon dioxide emissions. The research investigated how mid-ocean ridges and 43 ocean island volcanoes responded to these glacial sea level changes.
The 80,000-year-old atmospheric exception
While global average temperatures and atmospheric carbon dioxide concentrations usually move in tandem, scientists have identified irregularities in this relationship. An international team of researchers from the GEOMAR Helmholtz Centre for Ocean Research Kiel and the Alfred-Wegener-Institute Helmholtz Centre for Polar and Marine Research found that these trends can diverge.

Approximately 80,000 years ago, temperatures declined during a transition to glacial conditions, but atmospheric carbon dioxide levels remained relatively stable for several thousand years. Scientists believe enhanced volcanic activity, driven by falling sea levels, may have caused this stability.
For more on this story, see Diabetes: Hypertension drugs may speed up kidney disease.
This decoupling of temperature and CO2 levels is significant because it challenges the assumption that these two variables always move in a direct, synchronized relationship. The stability of CO2 during this period suggests that volcanic emissions provided a buffer, potentially slowing the rate of cooling by replenishing the atmosphere with greenhouse gases during the climate system’s descent into the last ice age.
The enhanced volcanic carbon dioxide flux may have stabilized the atmospheric carbon dioxide concentrations during the climate system’s descent into the last ice age.
Prof. Dr. Lars Rüpke of GEOMAR
Iron fertilization and ocean carbon storage
The relationship between volcanic activity and sea-level changes may also impact the ocean’s ability to manage carbon. According to a summary in Nature, sea-level falls can increase mid-ocean-ridge volcanism, which may lead to increased ocean iron fertilization and enhanced ocean carbon storage.

This process is closely linked to the “biological pump” in the ocean. Iron is a limiting nutrient for phytoplankton, the microscopic organisms responsible for much of the ocean’s carbon uptake. Increased volcanic activity can release hydrothermal fluids and volcanic ash, which are rich in iron. These nutrients stimulate phytoplankton blooms; as these organisms perform photosynthesis, they absorb CO2 from the atmosphere and, upon death, sink to the ocean floor, effectively sequestering carbon in the deep sea. This interaction between volcanism and ocean biology highlights the complexity of Earth’s feedback loops, as volcanic CO2 emissions and enhanced carbon sequestration can act as opposing forces in the climate system.
This follows our earlier report, Ces aliments pourraient davantage vous protéger du cancer du sein si vous les choisissez bio.
Research modeling and geological timelines
To quantify these processes, the research team developed a computer model integrated with geodynamic data. They also analyzed paleo-climate data and conducted simulations using a model of the global carbon cycle, as reported by ScienceDaily.
To better understand and quantify these processes, we developed a comprehensive computer model that we integrated with geodynamic data. In addition to this we analyzed paleo-climate data and carried out simulations with a model of the global carbon cycle.
Dr. Jörg Hasenclever, lead author
Co-author Dr. Gregor Knorr of the Alfred-Wegener-Institute stated that these interactions provide a new component for earth system research to understand climate evolution during glacial sea level changes. The investigations suggest these interactions between the solid earth and the climate system occur on geologically short timescales of approximately 5,000 to 15,000 years.
The integration of geodynamic data is crucial because it provides a physical basis for the changes observed in the carbon cycle. This dual-layered approach allows scientists to simulate how physical changes in the Earth’s crust translate into chemical changes in the atmosphere and oceans over long-term geological cycles.